
“We’re too small to be hacked.” If you’ve said this or thought it while running a retail operation in Africa, this post is your wake up call. Written with full respect, zero condescension, and a genuine desire to keep your business intact.
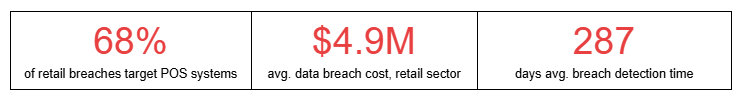
Let’s talk about the thing nobody in retail wants to admit: most businesses are not protecting customer data the way they think they are. Not the small boutiques. Not the mid sized chains. And honestly? Not even some of the bigger names that should know better.
We’re not saying this to scare you into buying something. We’re saying it because we’ve seen what happens when it goes wrong and it’s avoidable.
The Hack Doesn’t Start With a Genius in a Hoodie. It Starts With Your Cashier’s Email.
Hollywood has done cybersecurity a disservice. The image of a lone hacker cracking elite code makes the whole thing feel abstract and distant something that happens to banks and governments, not to your Westland’s branch or your Sandton flagship.
Here’s what actually happens. A staff member gets an email that looks like it’s from your POS vendor. They click. They type in their credentials. Now someone you’ve never met has access to your entire point-of-sale network. That’s it. No drama. No hoodies.
“Retail breaches don’t begin in your servers. They begin in your staff WhatsApp group, your shared passwords spreadsheet, and the vendor login you forgot to revoke when they finished the job three months ago.”

Five Things Happening Right Now in Your Business That Shouldn’t Be
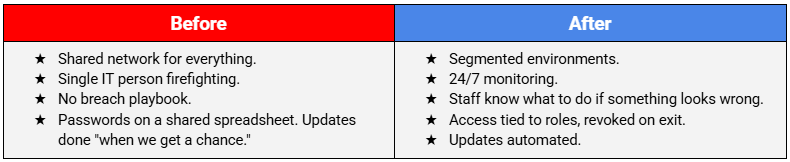
We’ve assessed retail environments across East and Southern Africa. The same gaps appear everywhere. Not because retailers are careless but because security was never designed into these systems from the start. Here’s what we keep finding:
- Customer Wi-Fi and payment networks share the same connection. Anyone on your guest Wi-Fi is technically on the same network as your card machines. That’s not a conspiracy theory it’s a configuration problem we see constantly.
- Former employees still have active login credentials. Staff turnover in retail is high. Security offboarding rarely keeps pace. Ex-staff access to internal systems is an industry wide problem nobody wants to talk about.
- Your loyalty app stores customer data in ways you haven’t fully reviewed. Third-party loyalty platforms collect names, phone numbers, purchase histories. When was the last time you checked their security certifications.
- POS firmware hasn’t been updated since the machines were installed. Manufacturers release security patches. They just don’t come with flashing lights demanding you install them.
- There’s no plan for what to do if something goes wrong. Not “no good plan.” No plan. Most retail operations have a fire drill procedure and zero breach response steps

“But We’re PCI Compliant.” Great. That’s the Floor, Not the Ceiling.
Compliance gets confused with security so often it’s almost its own crisis. PCI-DSS is important genuinely. It sets a minimum standard for handling card payments. But it’s exactly that: a minimum. It was designed to prevent the worst outcomes, not to protect against the current threat landscape.
The businesses that get breached while technically compliant aren’t rare anomalies. They’re a regular occurrence. Because compliance is about documentation and checkboxes. Security is about what happens at 2am on a public holiday when nobody’s watching.
What Actually Changes When You Get This Right.
This isn’t about building a fortress that makes your stores miserable to work in. The goal is to be invisible security that runs underneath everything, that your staff barely notice, and that makes it dramatically harder for attackers to succeed.
When it works well, your business manager stops getting phishing emails that look convincing. Your payment network becomes a completely separate environment from everything else. You know within minutes not months if something unusual is happening. And your customers’ data is actually protected, not just nominally so.
“The businesses that sleep well at night aren’t the ones with the most expensive locks. They’re the ones that stopped assuming it wouldn’t happen to them.”

So What Do You Actually Do Next?
Start with honesty. Not with a vendor pitch. Ask yourself: if someone wanted to get into our systems today, where would they start? Walk through your business with that question in mind. The answers will surprise you.
Then and this is the practical part get an independent security assessment done by someone with no interest in selling you the most expensive solution. Map your real exposure before you spend a single cent on new tools. Most retail operations don’t need more software. They need the software they already have configured correctly, and a set of habits that make breaches harder.
The retailers who get this right don’t become invincible. They become significantly less attractive targets than the shops next door. In security, that’s often enough.

Crystal Technologies works with retailers across sub-Saharan Africa to build security programmes that fit how retail actually operates not how it looks in an enterprise IT textbook. If any of this felt uncomfortably familiar, that’s a good sign.
Find out where your real gaps are before someone else does. Book a free 30 minute retail security conversation with the Crystal team and get your honest answers today.





 Chat with Us
Chat with Us